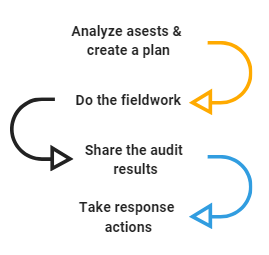
Four Basic Steps the Auditing Process Consists Of
Before the breach occurs ... or, well, the external auditor shows up at your doorstep, you'd better launch the in-house auditing program. Launching it from scratch can be bothersome and it's fine if you don't know where to start. This article does not focus on specific tools or auditing techniques but rather gives you a bird's eye view of the auditing process in general. Here are four basic steps a typical internal auditing process consists of.
- Analysis
- Conducting audit activities
- Reporting results
- Taking response actions
Analysis
What is the purpose of the audit? Why did you decide to conduct audit activities at first place? Do you have any other goals besides proving compliance? Who is interested in audit results? What kind of improvements are you looking for? As you answer these questions, you'll get a clearer understanding of how to start planning for audit activities.
First things first, your journey starts with determining the assets that need to be examined. These can be assets critical to your business such as files with important data or those assets that fall under various laws and regulations such as permissions and policies.
If your company operates in a regulated environment, you are likely to know the exact standards the company should be compliant with. For example, the company selling goods online transmits, stores, and processes cardholder data, hence it is subject to PCI DSS compliance assessment. Any healthcare service provider within the U.S. should be HIPAA compliant, etc. Each standard dictates the entities to be monitored, expected results, and control execution procedures.
If your company is not entitled to prove compliance in front of external auditors and compliance committees, you have more options while determining the auditing scope. Cygna Labs encourages you to research the data governance best practices and compliance standards to define the baselines and secure configuration settings. Try creating a list of auditing goals you want to achieve. For example, having zero passwords set to "never expire" or no folders with read/write access shared with "Everyone".
Once you figured out the auditing scope and its ideal configuration that you will later use to compare your data against, it's time for some fieldwork. Create a feasible auditing plan, schedule audit activities, and start assessing your corporate environment.
Conducting Audit Activities
To cut a long story short, just follow the plan you created. Review logs, check right assignments, analyze the Active Directory structure, monitor user activity, test controls, etc. There are many ways to get this work done. You can use native auditing tools (e.g., Event Viewer) or opt for comprehensive auditing solutions such as Cygna Auditor. Right now, your goal is to collect as much data about your critical assets as you need to evaluate security and compliance with various standards and regulations. Note that auditing activities will take a while since you need to accumulate data over time.
If you happen to use Cygna Auditor, set up data collection and enjoy the flexibility of auditing options. Search feature enables you to drill down to details and investigate potentially insecure cases. Built-in reports are designed to answer most compliance-related questions, such as were there any password resets or changes to administrative groups. With Cygna Auditor, you will be able to corroborate that activity in your corporate environment is traceable and accountable at any moment in time.
Reporting Results
Sharing inspection results is essential if you want to keep your organization infrastructure secure and efficient. Even if auditors are not at your doorstep, there are people in your organization who will definitely benefit from knowing the internal audit results.
As an internal auditor, step out and schedule a series of meetings where you will share the audit results. Provide reports for stakeholders, describe the current state and the security strategy. Conduct meetings with administrators and other security-related departments where you will share the auditing goals, discuss the actual bottlenecks and problem points, and finally encourage others to be proactive when it comes to data governance. You can even make a presentation for regular users—office clerks and managers—to spread the knowledge why the security and accountability matter.
Taking Response Actions
By now, you may already know your company's infrastructure weak points and assets that require your immediate attention. Without further ado, start implementing the security strategy—enforce new policies, update permissions, work towards reaching your auditing goals and state recommended by industry best practices and compliance standards.
What is Next?
Starting an auditing journey can never be easy. Make sure to schedule multiple revisions, don't be afraid to adjust your techniques, auditing scope, or auditing goals. With each iteration, write down the results and especially the insights you gained. Create your own auditing knowledge base by documenting the current guidelines and requirements. Finally, keep up to date with the security best practices and recognized industry standards and regulations but remember to tailor them to your organization's specific needs.
